this post was submitted on 19 Jul 2024
1283 points (99.4% liked)
Programmer Humor
19706 readers
124 users here now
Welcome to Programmer Humor!
This is a place where you can post jokes, memes, humor, etc. related to programming!
For sharing awful code theres also Programming Horror.
Rules
- Keep content in english
- No advertisements
- Posts must be related to programming or programmer topics
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
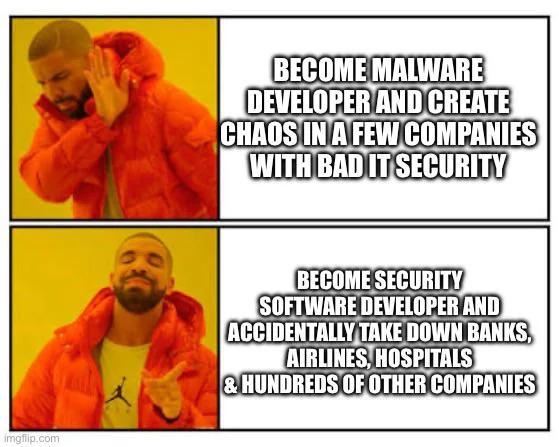
ItS NoT A wInDoWs PrObLeM -- Idiots, even on Lemmy
I genuinely can't tell at whom you are addressing this. Those claiming it is a Windows problem or those that say otherwise?
You can not like windows, and also recognize that CrowdStrike isn't from Microsoft - so a problem that CrowdStrike caused isn't the fault of Windows.
If that makes me a idiot by holding two different ideas in my head, so be it, but you are spending time with us, so thank you for elevating us!
I'm sorry, but distinguishing between different concepts is forbidden here. You go straight to jail.
I'm waiting for the post mortem before declaring this to not be anything to do with MS tbh. It's only affecting windows systems and it wouldn't be the first time dumb architectural decisions on their part have caused issues (why not run the whole GUI in kernel space? What's the worst that could happen?)
I agree it's possible. But if you're a software as a service vendor, it is your responsibility to be in the alpha and beta release channels, so if there is a show stopping error coming down the pipeline you can get in front of it.
But more tellingly, we have not seen Windows boot loop today from other vendors, only this vendor. Right now the balance of probabilities is in the direction of crowd strike
Ah yes the classic presumption of guilt, a keystone of justice
I'm not sure how to break this to you but this is just an internet forum, not a court of law
The reason courts use it is because they value having true opinions. But you're welcome to not value that indeed
The reason courts have rules of how convinced one must be to declare guilt is because they dread punishing an innocent over allowing a guilty person free
We aren't in a position to hurt the probably guilty party so it doesn't matter a bit of we jump to conclusions unfairly
Hi, idiot here. Can you explain how it is a windows problem?
It's a problem affecting Windows, not problem caused by Windows I guess.
That's what I was thinking so I was curious what the argument would be
If you patch a security vulnerability, who's fault is the vulnerability? If the OS didn't suck, why does it need a 90 billion dollar operation to unfuck it?
Redhat is VALUED at less than that.
https://pitchbook.com/profiles/company/41182-21
It's a fucking windows problem.
Sure, but they weren't patching a windows vulnerability, windows software, or a security issue, they were updating their software.
I'm all for blaming Microsoft for shit, but "third party software update causes boot problem" isn't exactly anything they caused or did.
You also missed that the same software is deployed on Mac and Linux hosts.
Hell, they specifically call out their redhat partnership: https://www.crowdstrike.com/partners/falcon-for-red-hat/
Crowdstrike completely screwed the pooch with this deploy but ideally, Windows wouldn’t get crashed by a bas 3rd party software update. Although, the crashes may be by design in a way. If you don’t want your machine running without the security software running, and if the security software is buggy and won’t start up, maybe the safest thing is to not start up?
Are we acting like Linux couldn't have the same thing happen to it? There are plenty of things that can break boot.
CrowdStrike also supports Linux and if they fucked up a Windows patch, they could very well fuck up a linux one too. If they ever pushed a broken update on Linux endpoints, it could very well cause a kernel panic.
Yeah, it's a crowd strike issue. The software is essentially a kernel module, and a borked kernel module will have a lot of opportunities to ruin stuff, regardless of the OS.
Ideally, you want your failure mode to be configurable, since things like hospitals would often rather a failure with the security system keep the medical record access available. :/. If they're to the point of touching system files, you're pretty close to "game over" for most security contexts unfortunately. Some fun things you can do with hardware encryption modules for some cases, but at that point you're limiting damage more than preventing a breach.
Architecture wise, the windows hybrid kernel model is potentially more stable in the face of the "bad kernel module" sort of thing since a driver or module can fail without taking out the rest of the system. In practice.... Not usually since your video card shiting the bed is gonna ruin your day regardless.
How the fuck did my Fedora just bluescreen?? Crowdstrike!
*audience laughter, freeze-frame*
Are the Mac and Linux machines having BSOD (-style) issues and trouble booting?
No, because CrowdStrike didn't bork the drivers for those systems. They could have, though.
Nope, because they only shipped a corrupted windows kernel module.
It's dumb luck that whatever process resulted in them shipping a broken build didn't impact the other platforms.
They've got Paid BSOD, I've got FreeBSD, we're not the same.
isn't XNU more decoupled than Windows kernel?
"even on Lemmy"
Like this is some highbrow collection of geniuses here?
No just statistically we are all Arch (btw) Linux users who hate Windows.
Because it isn't. Their Linux sensor also uses a kernel driver, which means they could have just as easily caused a looping kernel panic on every Linux device it's installed on.
There's no way of knowing that, though. Perhaps their Linux and Darwin drivers wouldn't have paniced the system?
Regardless, doing almost anything at the kernel level is never a good idea
It's not impossible. Crowdstrike has done it recently to linux machines.
Kernel panic observed after booting 5.14.0-427.13.1.el9_4.x86_64 by falcon-sensor process:
https://access.redhat.com/solutions/7068083
Paywalled, unfortunately
Also, it's less about "their" drivers and more about what a kernel module can do.
Saying "there's no way to know" doesn't fit, because we do know that a malformed kernel module can destabilize a linux or mac system.
"Malformed file" isn't a programming defect or something you can fix by having a better API.
Having the data exposed to userspace via an API would avoid having to have a kernel module at all... Which when malformed wouldn't compromise the kernel.
I mean, sure. But typically operating systems don't expose that type of information to user space, instead providing a kernel interface with user mode configuration.
It's why they use the same basic approach on mac and Linux.
Security operations being one of the things that is often best done at the kernel level because of the need to monitor network and file operations in a way you can't in user mode.