Lemmy Shitpost
Welcome to Lemmy Shitpost. Here you can shitpost to your hearts content.
Anything and everything goes. Memes, Jokes, Vents and Banter. Though we still have to comply with lemmy.world instance rules. So behave!
Rules:
1. Be Respectful
Refrain from using harmful language pertaining to a protected characteristic: e.g. race, gender, sexuality, disability or religion.
Refrain from being argumentative when responding or commenting to posts/replies. Personal attacks are not welcome here.
...
2. No Illegal Content
Content that violates the law. Any post/comment found to be in breach of common law will be removed and given to the authorities if required.
That means:
-No promoting violence/threats against any individuals
-No CSA content or Revenge Porn
-No sharing private/personal information (Doxxing)
...
3. No Spam
Posting the same post, no matter the intent is against the rules.
-If you have posted content, please refrain from re-posting said content within this community.
-Do not spam posts with intent to harass, annoy, bully, advertise, scam or harm this community.
-No posting Scams/Advertisements/Phishing Links/IP Grabbers
-No Bots, Bots will be banned from the community.
...
4. No Porn/Explicit
Content
-Do not post explicit content. Lemmy.World is not the instance for NSFW content.
-Do not post Gore or Shock Content.
...
5. No Enciting Harassment,
Brigading, Doxxing or Witch Hunts
-Do not Brigade other Communities
-No calls to action against other communities/users within Lemmy or outside of Lemmy.
-No Witch Hunts against users/communities.
-No content that harasses members within or outside of the community.
...
6. NSFW should be behind NSFW tags.
-Content that is NSFW should be behind NSFW tags.
-Content that might be distressing should be kept behind NSFW tags.
...
If you see content that is a breach of the rules, please flag and report the comment and a moderator will take action where they can.
Also check out:
Partnered Communities:
1.Memes
10.LinuxMemes (Linux themed memes)
Reach out to
All communities included on the sidebar are to be made in compliance with the instance rules. Striker
view the rest of the comments
No. You admitted those words mean nothing to you.
You plan for each eventually and ensure all responsibilities are understood.
Multisignature, limit controlled wallets
Wait for a few blocks before assuming your transaction is confirmed. Don't be dishonest during a fork event.
The general public is woefully uneducated and unsupported for blockchain managed finances, but the technology is fine.
I have literally explained to you what I meant, there is nothing to admit, lmao.
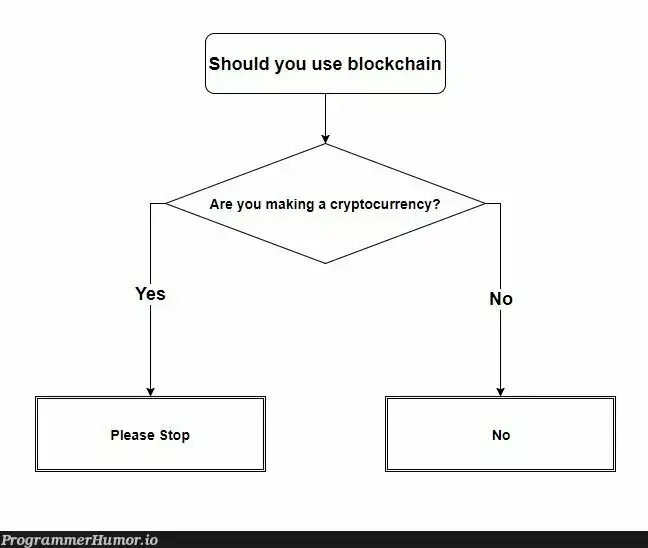
This is the issue with cryptobros you just think you are so much smarter than everyone else, and everyone else must be stupid and just not understand how crypto works.
Meanwhile you cant even see the huge flaws with the technology, you think " just wait and don't be dishonest" while there is a disagreement and unrecoverable split in the network is a viable solution... fucking hell that's such a childish take
When was last time a fork caused an unforseen problem in a popular blockchain?
There are plenty of things about blockchain technology you could have mentioned that are not yet perfect (privacy, scalability, accessibility, governance, regulation, interoperability etc.) but the best attack you have is that cryptography is meaningless.