this post was submitted on 28 Apr 2024
29 points (78.4% liked)
Security
5014 readers
1 users here now
Confidentiality Integrity Availability
founded 4 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
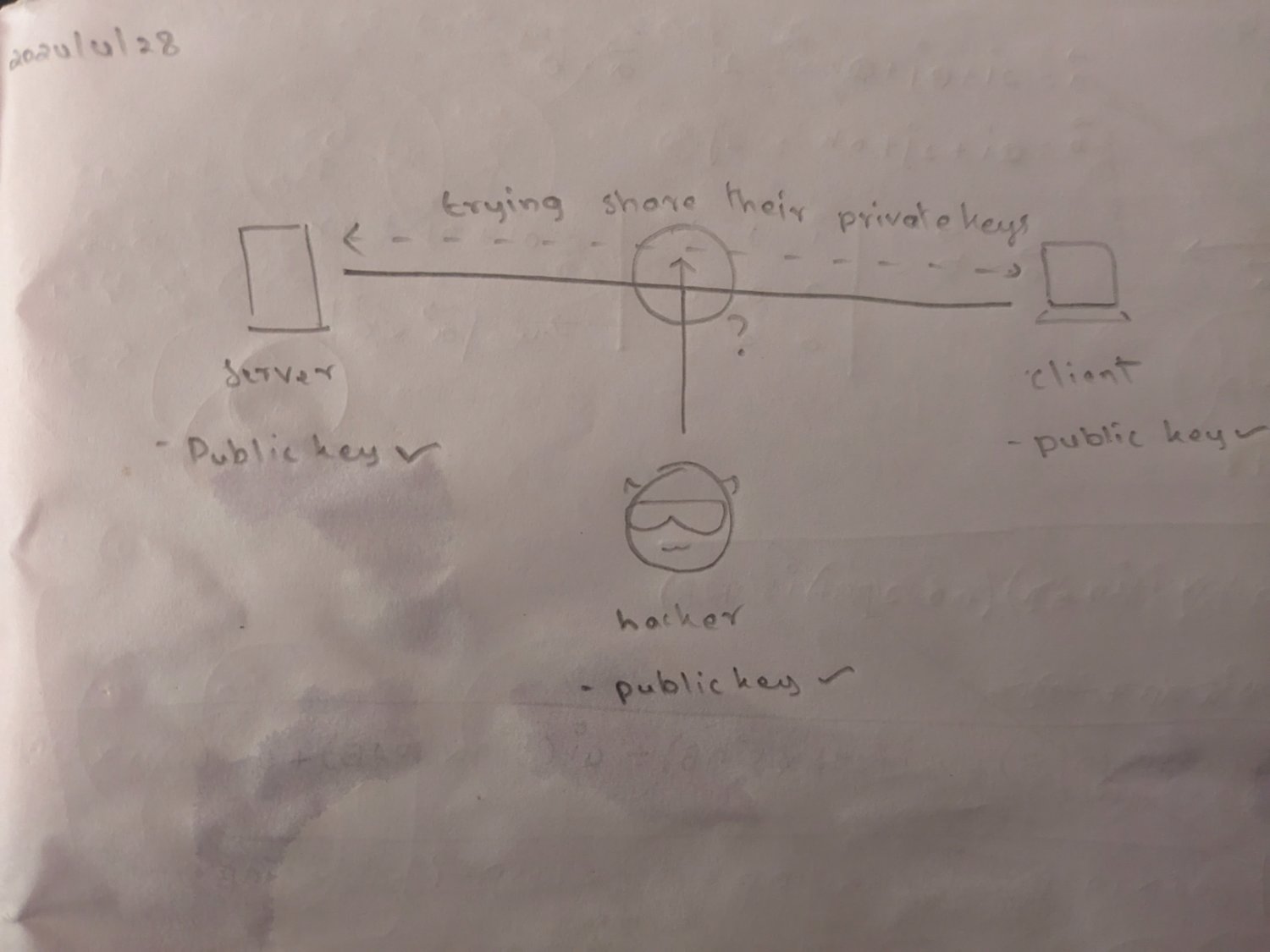
This is incorrect, for asymmetric (public-private) encryption. You never, ever share the private key, hence the name.
The private key is only used on your system for local decryption (someone sent a message encrypted with your public key) or for digital signature (you sign a document with your private key, which can be validated by anyone with your public key).
For the server, they are signing their handshake request with a certificate issued by a known certificate authority (aka, CA, a trusted third party). This prevents a man-in-the-middle attack, as long as you trust the CA.
The current gap is in inconsistent implementation of Organization Validation/Extended Validation (OV/EV), where an issuer will first validate that domains are legitimate for a registered business. This is to help prevent phishing domains, who will be operating with TLS, but on a near-name match domain (www.app1e.com or www.apple.zip instead of www.apple.com). Even this isn’t perfect, as business names are typically only unique within the country/province/state that issues the business license, or needed to be enforced by trademark, so at the end of the day, you still need to put some trust in the CA.