this post was submitted on 07 Apr 2024
497 points (95.6% liked)
Security
5431 readers
1 users here now
Confidentiality Integrity Availability
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
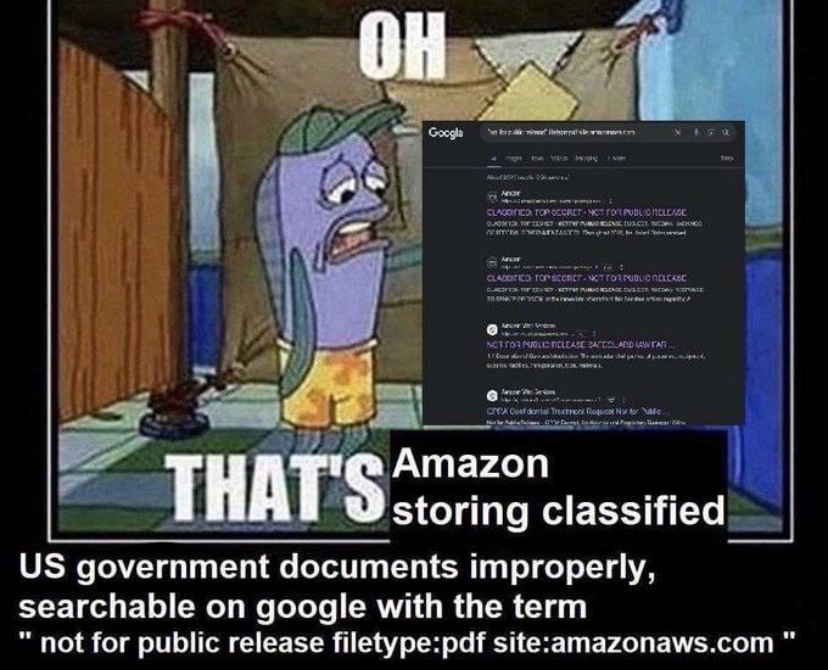
What's the over-under on this being a honeypot?
My bets are on ~~"cloud infrastructure is bad for highly secret information" rather than "public web honeypot with zero obfuscation"~~ Edit: likely fake. The sensationalist in me would love it if this was real because it would confirm my "cloud storage bad" biases, but alas, the document markings dont appear to be consistent with my understanding of official US Government confidentiality/secrecy markings
If S3, it's not cloud storage's fault some dummies enable public access to buckets which is disabled by default.
Youre correct it's not the provider's fault, but it's much harder in my very biased opinion to accidentally expose a secure 100% internal intranet than it is to accidentally put a top secret document in a public data bucket.
But it's a moot argument in this case anyway. Fake documents means these are likely exposed just to troll folks like us.