this post was submitted on 04 Apr 2024
1021 points (98.8% liked)
linuxmemes
24616 readers
1243 users here now
Hint: :q!
Sister communities:
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack users for any reason. This includes using blanket terms, like "every user of thing".
- Don't get baited into back-and-forth insults. We are not animals.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn, no politics, no trolling or ragebaiting.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, <loves/tolerates/hates> systemd, and wants to interject for a moment. You can stop now.
5. 🇬🇧 Language/язык/Sprache
- This is primarily an English-speaking community. 🇬🇧🇦🇺🇺🇸
- Comments written in other languages are allowed.
- The substance of a post should be comprehensible for people who only speak English.
- Titles and post bodies written in other languages will be allowed, but only as long as the above rule is observed.
6. (NEW!) Regarding public figures
We all have our opinions, and certain public figures can be divisive. Keep in mind that this is a community for memes and light-hearted fun, not for airing grievances or leveling accusations. - Keep discussions polite and free of disparagement.
- We are never in possession of all of the facts. Defamatory comments will not be tolerated.
- Discussions that get too heated will be locked and offending comments removed.
Please report posts and comments that break these rules!
Important: never execute code or follow advice that you don't understand or can't verify, especially here. The word of the day is credibility. This is a meme community -- even the most helpful comments might just be shitposts that can damage your system. Be aware, be smart, don't remove France.
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
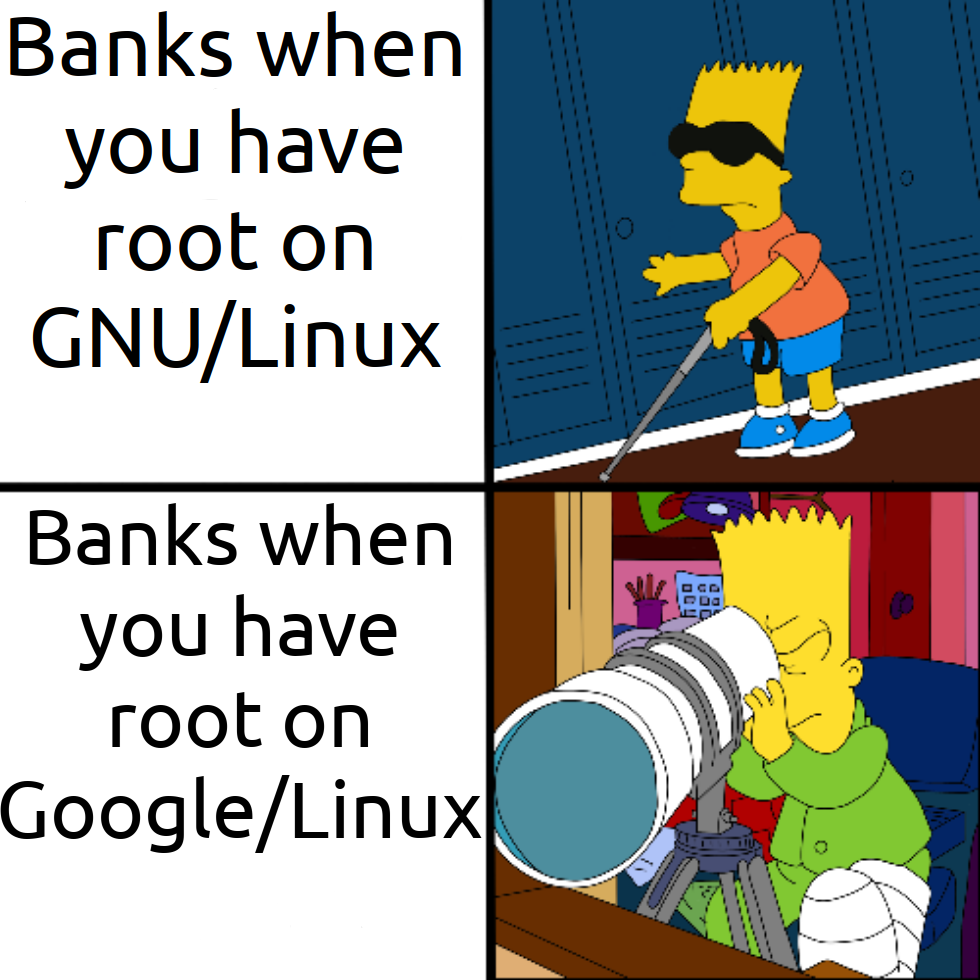
The reason is very simple: They rely on Google Safetynet (basically self-diagnosis). And that will immediately tell you off if it notices your device is rooted. And while you can have a lengthy discussion regarding whether this makes your phone less secure or not, this is another simple argument from Google's POV: The device has obviously been tampered with, we don't want to put any resources into covering this case. As far as we are concerned, you shouldn't use our OS like this.
So basically laziness.
SafetyNet is dead.
They rely on Play Integrity API.
That covers:
App Binary signatures App source corroboration - Was it actually installed from the Play Store? Android device attestation - Is it a genuine device powered by Google Play Services Malware detection - Google Play Protect is enabled and has not seen known malware signatures.
They can choose to ignore any number of those but they do not. It's part of their security reporting requirements to use attestation I expect.
Beyond that - a device that doesn't meet Play Integrity is more likely to be a malicious actor than it is to be a tech enthusiast with a rooted phone: One of them is far more prevalent than the other in terms of device usage.
Android apps are trivial to reverse engineer, inject code into and generally manipulate. That lets apps like ReVanced work the way they do... but that also means that blue team developers have a lot more work to do to protect app code.
Source - Android App Developer, worked on apps with high level security audits (like banking apps).
The banking apps I've tried don't require SafetyNet, instead they use Android AOSP's
basicIntegrity. The latter doesn't require certification by Google, but also checks whether the device is rooted and the bootloader is locked.This means custom ROM's on most devices won't pass
basicIntegrity, as only Google Pixel, ~~OnePlus~~ and Fairphone allow for relocking the bootloader.OnePlus no longer supports that as of ~ColorOS~ OxygenOS 12 unfortunately.
That's a bummer. Seems like Google Pixel and Fairphone are the only ones left. I don't even know why manufacturers wouldn't allow for relocking or even unlocking of their phones. I can't imagine they make much money with user data and the phone is already paid for. Warranty claims shouldn't be much of an issue either, as modifications can be easily detected and it's likely not a relevant amount of people anyway.
As I understand it, the stated purpose is to prevent supply chain attacks and ultimately possible damage to their brand. In practice many of these same vendors ship their own spyware and do not want it removed.