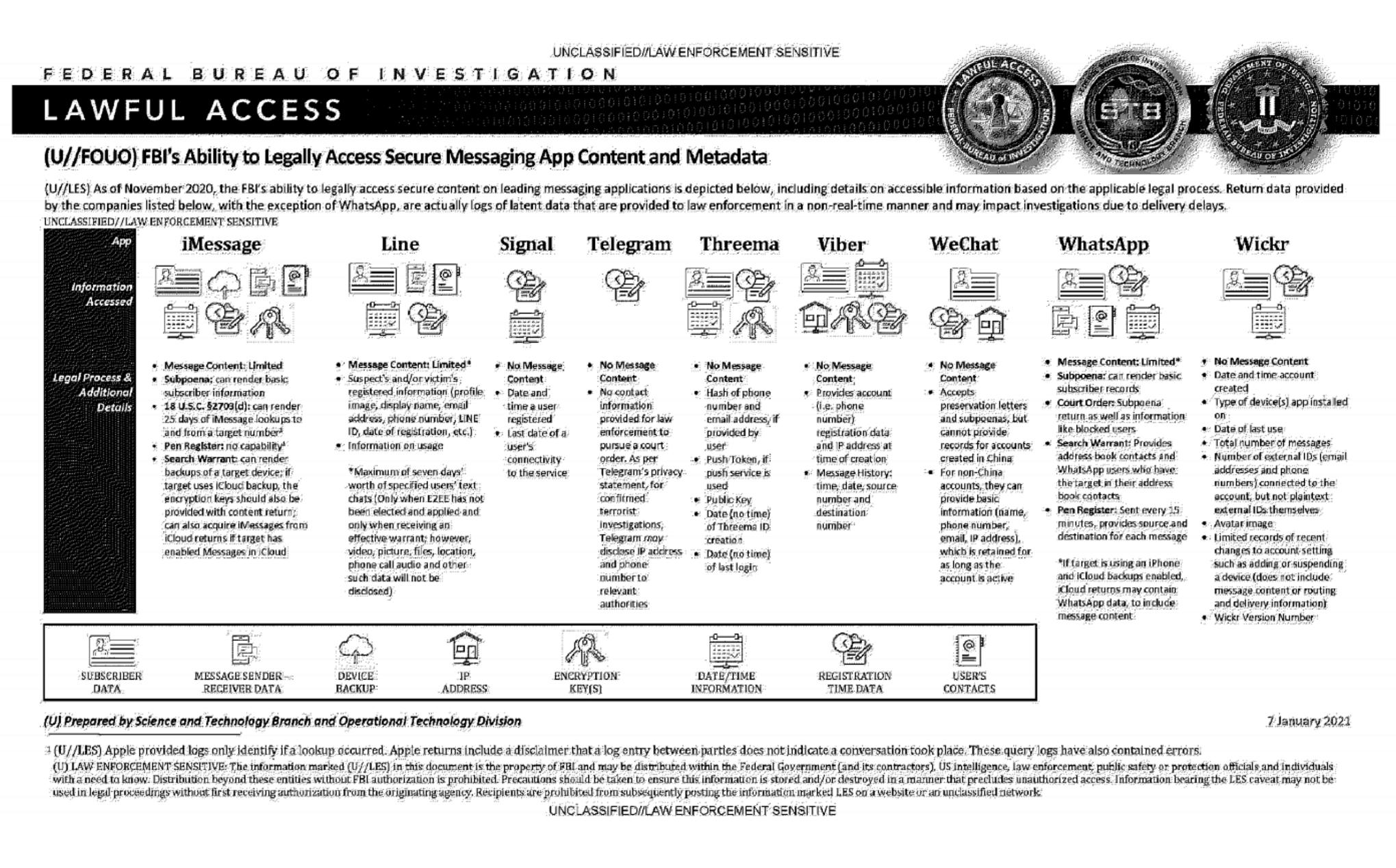
An official FBI document dated January 2021, obtained by the American association "Property of People" through the Freedom of Information Act.
This document summarizes the possibilities for legal access to data from nine instant messaging services: iMessage, Line, Signal, Telegram, Threema, Viber, WeChat, WhatsApp and Wickr. For each software, different judicial methods are explored, such as subpoena, search warrant, active collection of communications metadata ("Pen Register") or connection data retention law ("18 USC§2703"). Here, in essence, is the information the FBI says it can retrieve:
-
Apple iMessage: basic subscriber data; in the case of an iPhone user, investigators may be able to get their hands on message content if the user uses iCloud to synchronize iMessage messages or to back up data on their phone.
-
Line: account data (image, username, e-mail address, phone number, Line ID, creation date, usage data, etc.); if the user has not activated end-to-end encryption, investigators can retrieve the texts of exchanges over a seven-day period, but not other data (audio, video, images, location).
-
Signal: date and time of account creation and date of last connection.
-
Telegram: IP address and phone number for investigations into confirmed terrorists, otherwise nothing.
-
Threema: cryptographic fingerprint of phone number and e-mail address, push service tokens if used, public key, account creation date, last connection date.
-
Viber: account data and IP address used to create the account; investigators can also access message history (date, time, source, destination).
-
WeChat: basic data such as name, phone number, e-mail and IP address, but only for non-Chinese users.
-
WhatsApp: the targeted person's basic data, address book and contacts who have the targeted person in their address book; it is possible to collect message metadata in real time ("Pen Register"); message content can be retrieved via iCloud backups.
-
Wickr: Date and time of account creation, types of terminal on which the application is installed, date of last connection, number of messages exchanged, external identifiers associated with the account (e-mail addresses, telephone numbers), avatar image, data linked to adding or deleting.
TL;DR Signal is the messaging system that provides the least information to investigators.
No mention of Matrix. Wonder if it's not on their radar, or they have nothing, or just wasn't important to put it on there?
I'm wondering the same thing.
I am a long time signal user but I just started using Matrix yesterday and now I'm very curious about whether Signal or Matrix is better somehow in terms of security/privacy.
I stopped using Signal after they said no alternate clients, then got into crypto, then introduce a proprietary shim to their stack.
I plan on someday actually running my own Matrix server for myself and family, right now I'm on Matrix.org though. At this point I don't know how folks recommend Signal over Matrix. There are a lot of clients, so maybe the choice of clients is too confusing? IDK.
But anyone saying Matrix isn't easy enough for non-tech folks to understand, my sister, niece, even wife set up Element themselves on their phones without issue. My father and step-mother both use Element with us. I configured it but they know how to message and do video chat and things.
Thanks for sharing! I really want to get my family on Matrix now.
We have not been able to find a solid chat/video call app that the entire family (various ages and tech aptitude) can effectively use. We've been bouncing around to various apps since COVID lockdowns started. We had been using Slack for a while but the video calling in Slack is unusable now.
We do voice and video chat every week with my family and it seems to work incredibly well. No real issues with any of it.
While France isn't a part of FVEY "the five eyes alliance", it is extremely likely that it is compromised because Matrix was created by the French government in 2018.
Keep in mind that op's foia request is from 2021.
Fact check: the French govt did not create Matrix.
Matrix is an open protocol created in 2014, for an Israel-based private company.
In 2018 the french govt decided to use a verson of that protocol in their own chatting network.
Thanks, and apologies. I've edited out my idiocy. Misremembered, and was thinking of something else.
Well, there are a few leakage issues with Matrix, but there’s also the benefit that you can stand up your own server or use one based in a country you’re comfortable having access to your basic connection data.
So unlike Signal where the hashes are all stored in one place, with Matrix no single government has control over the entire network.
I think it is because it is a bit nuanced. I used to host a matrix server and if the FBI was like hey, give us the data to something.
I’d just give them anything they wanted. I did not allow signups, I only gave access to one friend and only had it setup as a learning project.
I’m sure my friend wouldn’t do anything shady on it, I’ve been close friends with him for about 30 years. But I’m not going to fight the fbi on their behalf. Plus, if they were using the server for something that the fbi needed to get involved with, I’d be pissed they used my server to do it.
tl:dr anyone can host a matrix instance and each host could have different levels of access.
Also important to note it's been well known the CIA uses Matrix internally for communications. If they're using it for communication it's probably pretty sturdy.
I think it is because it is a bit nuanced. I used to host a matrix server and if the FBI was like hey, give us the data to something.
I’d just give them anything they wanted. I did not allow signups, I only gave access to one friend and only had it setup as a learning project.
I’m sure my friend wouldn’t do anything shady on it, I’ve been close friends with him for about 30 years. But I’m not going to fight the fbi on their behalf. Plus, if they were using the server for something that the fbi needed to get involved with, I’d be pissed they used my server to do it.
tl:dr anyone can host a matrix instance and each host could have different levels of access.
The server shouldnt be seeing anything of value if you're end to end encrypted
That is what I imagine as well. Either way, if they want files to try and decrypt then they can have them.