this post was submitted on 12 Dec 2024
408 points (94.7% liked)
linuxmemes
25025 readers
2431 users here now
Hint: :q!
Sister communities:
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack users for any reason. This includes using blanket terms, like "every user of thing".
- Don't get baited into back-and-forth insults. We are not animals.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn, no politics, no trolling or ragebaiting.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, <loves/tolerates/hates> systemd, and wants to interject for a moment. You can stop now.
5. 🇬🇧 Language/язык/Sprache
- This is primarily an English-speaking community. 🇬🇧🇦🇺🇺🇸
- Comments written in other languages are allowed.
- The substance of a post should be comprehensible for people who only speak English.
- Titles and post bodies written in other languages will be allowed, but only as long as the above rule is observed.
6. (NEW!) Regarding public figures
We all have our opinions, and certain public figures can be divisive. Keep in mind that this is a community for memes and light-hearted fun, not for airing grievances or leveling accusations. - Keep discussions polite and free of disparagement.
- We are never in possession of all of the facts. Defamatory comments will not be tolerated.
- Discussions that get too heated will be locked and offending comments removed.
Please report posts and comments that break these rules!
Important: never execute code or follow advice that you don't understand or can't verify, especially here. The word of the day is credibility. This is a meme community -- even the most helpful comments might just be shitposts that can damage your system. Be aware, be smart, don't remove France.
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
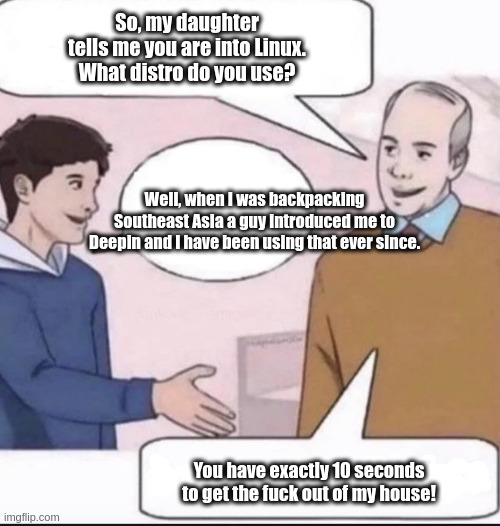
It’s by a Chinese company, and collects telemetry on its users via Umeng+, which is a Beijing-based analytics company. Even though it’s open source, the code is large enough that it’s hard to tell if there is anythinf compromising in there from the Chinese government, and/or whether/what data collected by Umeng+ is making it to the Chinese government.
It's unfortunate, because I really like the DE. Real stand out. If it were more trustworthy, it'd be my first choice.
Apparently you can download it from the AUR if you really want to.
So I guess the backdoor is buried DeepIn the code
I mean a simple
grep -r "string" *
Does wonders to find anything, but you need to know what you're looking for. I'd probably look for DNS names that end in government or China specific TLDs to start with.
grep -r "evil spyware" *nothing? awesome, I guess this software is safe to use. Let's gooo
I know you're be facetious here and I'm ignorant to actual application security methodology. I do have to ask though, when you are looking for something in code that could be a security risk, isn't it possible to look for methods or functions used to lookup DNS, outbound network calls, or even libraries used to obfuscate code? It seems to me that most programmers wouldn't go through lengths to obfuscate their code and would want it to be readable/maintainable, so doing so would be a red flag.
Obviously no one is going to search for "evil spyware" when auditing code. Your point stands it is not as simple as that.
You're totally right, I just think you underestimate how long it takes to rigorously audit a whole codebase. Let's say you look for outvound network calls. Now you need to figure out for all of them whether they are malicious, which will require specific domain knowledge. And that's assuming you find them all, the network call could be hidden away in a dependency. None of this is impossible but it requires a serious effort.
it's trivial to break that approach by obfuscating strings. You can do things like using base64 encoded strings in the source code, building strings from smaller component parts, or using rot13 on, say, the host component of a URI. That last one could be pretty interesting if you, as a threat actor, owned both permutations. The hostname (minus TLD) in the source code could be the nice, human readable version (www.happysite.org) that appears to be something legit. Then, when you rot13 it to www.uncclfvgr.org, traffic is sent to the evil site doing scary things. People can be far more tricksy than that. There's also the whole issue around whether or not the binaries you're running actually match the code in the repo. The xz kerfuffle showed how much can be hidden that way.
EDIT: I should make it clear that I don't use Deepin or the DE it provides because I only use WMs with no desktop, so the distro and DE are of no interest to me. I don't know if it's a security hazard or not, I have no horse in this fight.
There are so many ways to obfuscate things that your approach won't work.