In celebration of Bitcoin Black Friday 2023, we're offering a 10% discount on all BusKill cables sold between Nov 18 to Dec 03.
What is BusKill?
BusKill is a laptop kill-cord. It's a USB cable with a magnetic breakaway that you attach to your body and connect to your computer.
If the connection between you to your computer is severed, then your device will lock, shutdown, or shred its encryption keys -- thus keeping your encrypted data safe from thieves that steal your device.
What is Bitcoin Black Friday?
Black Friday is ~1 month before Christmas, and it's the busiest shopping day in the US. The first "Bitcoin Friday" (launched by Jon Holmquist) was Nov 9th, 2012 (at the time, one bitcoin was ~$11). The following year, the two ideas merged to become Bitcoin Black Friday.
This year, we're joining Bitcoin Black Friday by offering our products at a 10% discount if you pay with cryptocurrency.
Why should I use cryptocurrencies?
We've always accepted cryptocurrencies because:
- They're more secure than pre-cryptocurrency payment methods
- They're a more egalitarian system than pre-cryptocurrency finance
- They're more environmentally friendly than pre-cryptocurrency financial systems
- The fees are less than pre-cryptocurrency transactions
- They allow for anonymous purchases online
- Their transactions are censorship-resistant
Security
Before cryptocurrencies, making an online transaction was horrendously insecure and backwards.
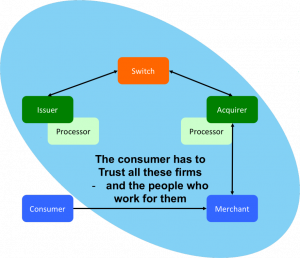
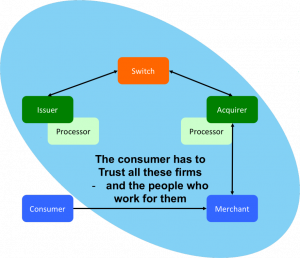 |
| "Conceptually, pull-based transactions are really not that different than giving three parties the password to your online banking service and trusting them to log in and take what they need. You have to trust the merchant, their IT supplier; the acquiring bank, their third-party processor; the card network; and your own card issuer---and everybody who works for them and has access to their systems. If a bad guy gets hold of your card details at any point in this process, they could drain your account. |
| The picture shows the scope of all the entities with access to your critical card information" source |
Asymmetric cryptography has been available since the 1970s, but CNP (Card Not Present) transactions to this day still don't use public keys to sign transactions. Rather, you give your private keys (that is, your credit card number, expiry, etc) directly to the merchant and you authorize them to pull money out of your account (trusting that they take the right amount and not to loose those precious credentials).
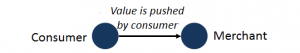
Bitcoin flipped this around to actually make transactions secure. With bitcoin, you don't give others the keys to take money out of your account. Instead, transactions are push-based. You sign a transaction with your private keys, and those keys are shared with no-one.
Even today, pre-cryptocurrency transactions are abhorrently insecure. In the US or Europe, if someone knows your account number and bank, they can direct debit money out of your account. For the same reason, losses due to credit card theft is enormous. To quote Satoshi Nakamoto's criticism of pre-cryptocurrency transactions, "A certain percentage of fraud is accepted as unavoidable"
In fact, fraudulent transactions in the banking industry are so common that your bank will generally reimburse your account for any malicious transactions that you tell them about within 60-90 days. But if someone drains your account of all your money and you don't notice for 12 months? Too bad. All your money is gone.
 |
| In Bitcoin, transactions are push-based. source |
Tokenization and 3DS are merely bandages on a fundamentally backwards, pull-based transaction model.
But because bitcoin is push-based, it's magnitudes more secure.
Egalitarian
If you have a bank account, then you probably take a lot of things for granted.
Like buying things online (with a credit card). Or getting cash when traveling abroad (from an ATM machine). Or taking out a loan so you can start a business.
Before crypto-currencies, it was very difficult to do these things unless you had a bank account. And in 2008 (the year with the first-ever bitcoin transaction), McKinsey & Company published a report concluding that half of the world's adult population is unbanked.
But with crypto-currencies, anyone with access to the internet and a computer or smart phone can use bitcoin to send and receive money online -- without needing to first obtain a bank account.
Environmentalism
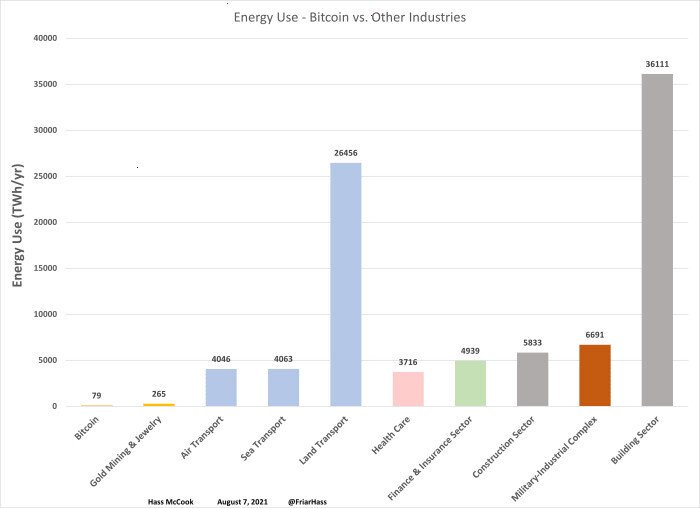
The energy required to facilitate transactions in decentralized, blockchain-based cryptocurrencies like bitcoin is minuscule by comparison. And, most importantly, the amount of energy used to solve the proof-of-work problem does not grow as the number of transactions-per-second grows.
Traditional financial institutions require an enormous amount of overhead to facilitate transactions in their centralized networks. Unlike bitcoin, which was designed specifically to eliminate the unnecessary overhead created by a trusted third party, pre-cryptocurrency transactions required humans to verify transactions. These humans require office buildings. These office buildings require energy to build and maintain. And, most importantly, as the number of transactions-per-second grows on their network, the number of humans and office space also grows.
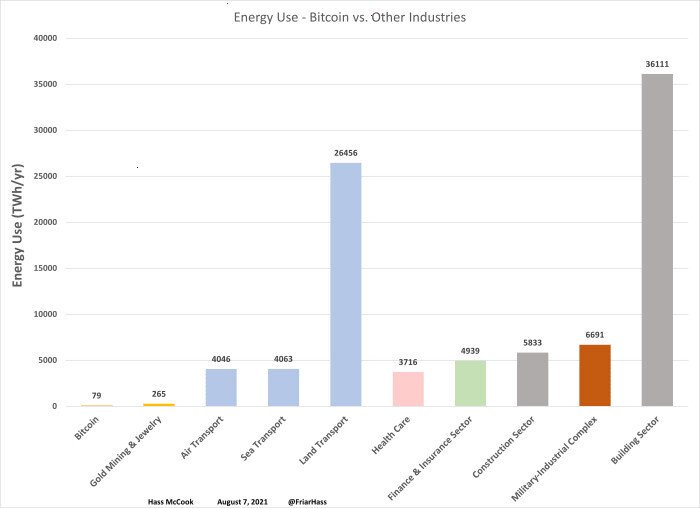 |
| Bitcoin versus other industries |
yearly energy use, in TWh source |
This fact is often misunderstood because there's a lot of misinformation on the Internet that makes a few disingenuous modifications to the facts:
- They calculate the energy usage of the computers processing transactions only, maliciously omitting calculating the energy usage of the entire industry's infrastructure (eg energy used by office buildings)
- They calculate the energy usage per transaction, maliciously omitting the fact that the amount of energy expended by bitcoin miners is automatically adjusted by the proof-of-work algorithm (so energy usage does not increase as the network scales-up)
- They offer statistics about "energy usage" without mentioning the energy sources. It matters if the energy source is coal/nuclear/natural-gas or solar/wind/hydroelectric
| "...estimates for what percentage of Bitcoin mining uses renewable energy vary widely. In December 2019, one report suggested that 73% of Bitcoin's energy consumption was carbon neutral, largely due to the abundance of hydro power in major mining hubs such as Southwest China and Scandinavia. On the other hand, the CCAF estimated in September 2020 that the figure is closer to 39%. But even if the lower number is correct, that's still almost twice as much [renewable energy sources] as the U.S. grid" |
 |
| source: Harvard Business Review |
Nic Carter |
The facts are that the energy usage of bitcoin is magnitudes less than the energy used by pre-cryptocurrency financial intuitions, that energy usage does not increase as the number of transactions processed by the network increases, and that mining bitcoin is often done with renewable energy.
The facts are that the energy usage of bitcoin is magnitudes less than the energy used by pre-cryptocurrency financial intuitions, that energy usage does not increase as the number of transactions processed by the network increases, and that mining bitcoin is often done with renewable energy.
Low Fees
The introduction to the Bitcoin White Paper (2008) clearly states that Bitcoin was created to reduce costs by using a distributed ledger (the blockchain) to eliminate the need for a trusted third party.
| "Commerce on the Internet has come to rely almost exclusively on financial institutions serving as trusted third parties to process electronic payments. While the system works well enough for most transactions, it still suffers from the inherent weaknesses of the trust based model. |
|
| Completely non-reversible transactions are not really possible, since financial institutions cannot avoid mediating disputes. The cost of mediation increases transaction costs... |
|
| These costs and payment uncertainties can be avoided in person by using physical currency, but no mechanism exists to make payments over a communications channel without a trusted party. |
|
| What is needed is an electronic payment system based on cryptographic proof instead of trust, allowing any two willing parties to transact directly with each other without the need for a trusted third party. Transactions that are computationally impractical to reverse would protect sellers from fraud, and routine escrow mechanisms could easily be implemented to protect buyers. In this paper, we propose a solution to the double-spending problem using a peer-to-peer distributed timestamp server to generate computational proof of the chronological order of transactions." |
 |
| source: Bitcoin Whitepaper |
Satoshi Nakamoto |
At the time of writing, the average transaction fee for a bitcoin transaction is $0.06. And unlike pre-cryptocurrency transactions, you can increase or decrease the fee that you pay to increase or decrease the time it takes for the transaction to complete (at $0.06, it will get added to the blockchain in ~1 hour).
By comparison, the way to send funds internationally through the Internet via pre-cryptocurrency banks is via an international wire transfer. Fees very per bank, but they typically charge $15-$85 per transaction. And unlike bitcoin, wire transfers won't make move on nights and weekends, so they can take 1-7 days to complete.
Also, with bitcoin, that $0.06 transaction fee only applies when you're sending money. Many banks will also charge a fee for an incoming wire transfer. In bitcoin, there is no transaction fee to receive money.
Anonymity
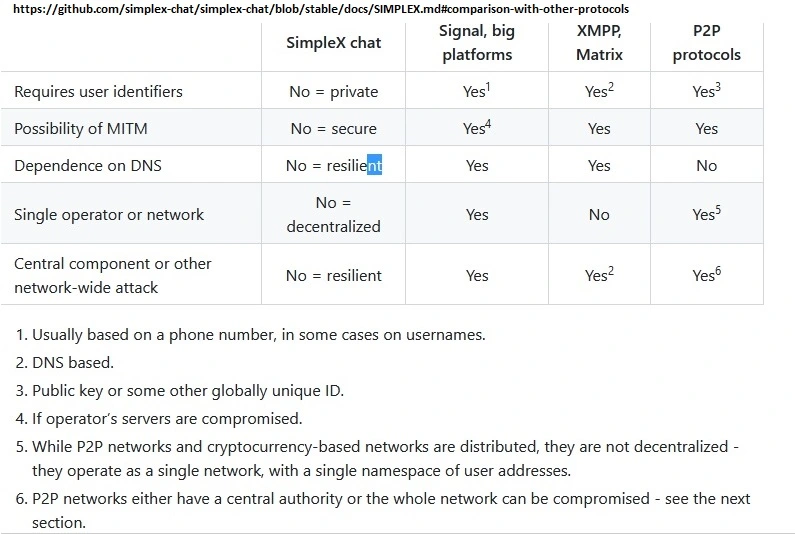
Though early cryptocurrencies like Bitcoin don't ensure anonymity like newer privacy coins, ZCash and Monero were designed specifically to provide private transactions.
This allows our customers to purchase from us anonymously, which can be extremely important for activists and journalists whose lives are threatened by their adversaries.
 |
| WikiLeaks started accepting donations in Bitcoin 7 months after PayPal froze their account |
We accept both ZCash and Monero. If you'd like us to accept another privacy coin, please contact us :)
Censorship-Resistant
Cryptocurrencies like bitcoin are peer-to-peer and permissionless. Transactions exchanging bitcoins occur directly between two parties. There is no middle-man that has the power to block, freeze, or reverse transactions.
Before blockchains were used to maintain a public ledger and enable peer-to-peer transactions, we were dependent on big financial institutions to move money on our behalf through the internet. That antiquated system allowed them to censor transactions, such as donations made to media outlets reporting war crimes and donations to protest movements.
| "For me, that is one of the coolest things about bitcoin... |
|
| People can potentially use it donate more anonymously to dissident groups and causes in a world where mass government surveillance threatens freedom of expression and certainly harms activists' ability to fundraise for their work, when people are afraid they could be targeted by a government for donating to a worthy cause." |
 |
| source |
Evan Greer |
After PayPal froze WikiLeaks's donation account in 2010, WikiLeaks started accepting bicoin in 2011.
From Occupy Wall Street to Ukraine, defenders of democracy have utilized permissionless cryptocurrencies to accept international donations without the risk of transactions made through financial institutions.
Buy BusKill with crypto
Don't risk loosing your crypto to a thief that steals your laptop. Get your own BusKill Cable at a 10% discount today!
Buy a BusKill Cable
https://buskill.in/buy
You can also buy a BusKill cable with bitcoin, monero, and other altcoins from our BusKill Store's .onion site.


Stay safe,
The BusKill Team
https://www.buskill.in/
http://www.buskillvampfih2iucxhit3qp36i2zzql3u6pmkeafvlxs3tlmot5yad.onion