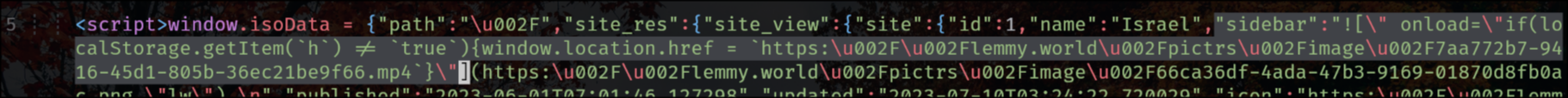
This has nothing to do with XSS, it is a simple HTML injection vulnerability, and it can only be exploited by instance admins.
Also Lemmy.world appears to have been running a custom frontend so it’s hard to say how widespread the affects of this are.