Hi,
If you don't know how work the chain of trust for the httpS
You might want to watch this video
https://invidious.privacydev.net/watch?v=qXLD2UHq2vk
( if you know a better one I'm all ears )
So in my point of view this system have some huge concerns !
- You need to relies to a preinstalled store certificate in your system or browser...
Yeah but do you know those peoples ??!! it might seem weird, but actually you should TRUST people that YOU TRUST/KNOW !!
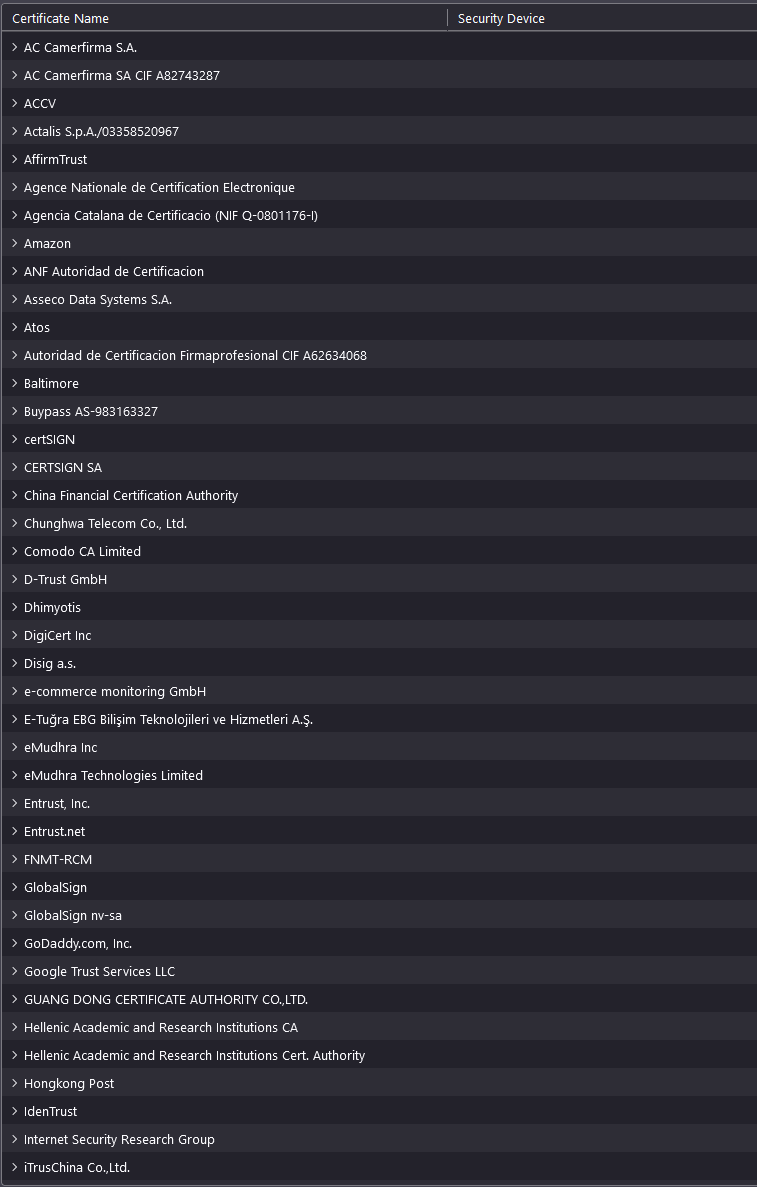
Here an extract from the certificate store om Firefox on Windows.
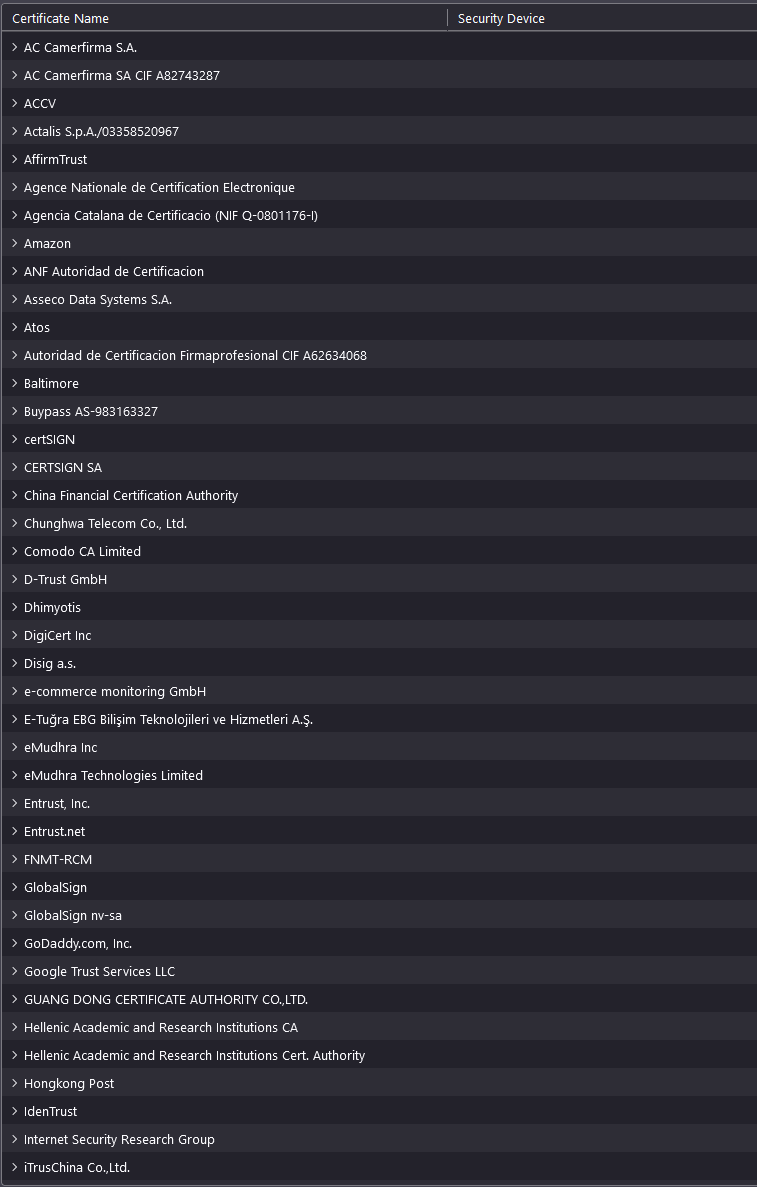
I do not know ( personally ) any of those COMMERCIAL company !
- Of course we could use Self-certificate but this is not protecting against Man-in-the-middle_attack . Instead of using a chain (so few 3th party involved , so increasing the attack surface ! ) why not using something simpler !? like for example
- a DNS record that hold the HASH of the public key of the certificate of the website !
- a decentralized or federated system where the browser could check those hash ?
Really I don't understand why we are still using a chain of trust that is
- not trusted
- increase the surface of attack
- super complex compare to my proposals ?
Cheers,
Why I don't use the term SSL
Because actually httpS now use TLS not anymore ssl
https://en.wikipedia.org/wiki/Transport_Layer_Security
and what about something like this.
The "verification servers" grab the public key directly from the Web server.
Any suggestions, ideas ?
How do you stop this? (Sorry I only have paint on this machine)
Computer/Network is compromised
User requests public key from Server
Hacker intercepts it, sends his own public key
User tries to connect with "verification" servers
Requests get redirected to compromised servers to OK the verification
User sends request to Server via Hacker with Hacker PubKey
Hacker decrypts it, re-signs it with Server PubKey
Sends it to server, gets response
Hacker decrypts server response, re-encrypts it with Hacker Private Key
Users receives message, can decrypt it with Hacker PubKey, everything looks normal
You're just substituting a local "Chain of Trust" with a server based trust system... Why would you trust that you can securely call the verification servers, and even if you can, why trust the verification servers?
If the computer of the Visitor is already compromised ! your simulation can stop there I think...
My scenario assume that the visitor computer is not compromised.
But let say his traffic get intercepted. Sure a hacker can send his PubKey (2) but in (3) the visitor (should) have already the PubKey of one (or few) verification server. So it should not be possible for an hacker to interfer with the communication (3) right ?